© David/BAl
This article was originally written and published in bahasa Indonesia on 24 May 2021.
Technological developments and advancements are increasingly sophisticated and appear in various systems on almost all lines. It causes the necessities of life to experience a significant increase. According to Rochmawan (2008), human needs are diverse but continue to grow endlessly in line with the development of civilization, science, and technology. In meeting their needs, humans continue to strive to optimize the satisfaction of their desires. Therefore, technology has become a significant aspect of meeting needs. Even when their needs have been met—but not by their desires—humans will continue to crave for more.
The human need for the satisfaction of material goods, which is in line with technological advances, makes the internet a media facility that is used not only for communication, but also to trade goods. This phenomenon is known as “online shopping.” With the synergy between marketing and information technology, e-commerce is created. E-commerce uses the internet, websites, and applications for digital business transactions between companies and individuals (Laudon et al., 2014). E-commerce can be an alternative option in buying and selling goods or services online. Consumers do not need to spend much energy, they only need to look at the website to make a transaction.
TEMASEK, a Singapore-owned SOE, and Google released The Opportunity of Indonesia (2017), which shows that the growth of e-commerce in Indonesian society is increasing along with the development of internet use in Indonesia. This increase has raised the value of the Indonesian e-commerce market. TEMASEK and Google predict that the value of the Indonesian e-commerce market will reach $81 billion by 2025 (Josephine et al., 2020).
Online shopping is a transaction carried out through media or intermediaries using internet access. This activity is carried out on various online buying and selling sites or social networks that provide traded goods and services. The advantages of shopping online can be categorized into four, namely convenience, information, available products and services, and cost and time efficiency (Harahap & Amanah, 2018). Those advantages are evident in the changing habit of people to shop online because of its convenience. People also think that e-commerce could quickly find the items they need, such as daily necessities, hobbies, etc.
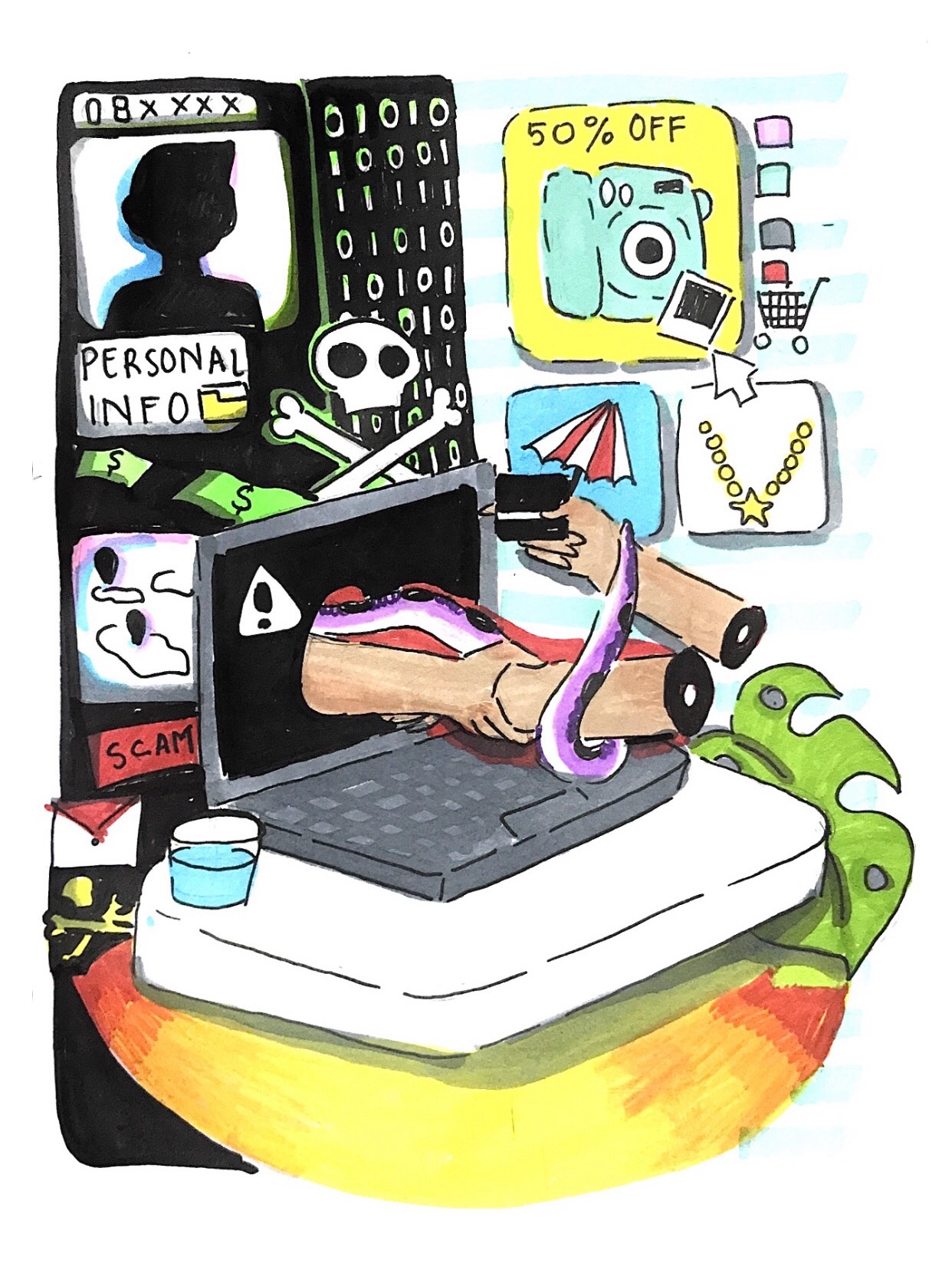
However, behind all the conveniences obtained, e-commerce also raises the issue of consumer concerns about the responsibility for personal data that has been recorded and collected in e-commerce companies. These personal datas are in the form of consumer identities, passwords, debit and credit card numbers, conversations in e-mail, as well as information related to consumer requests. In the study titled “Online Shopping Behavior in Indonesia: Case Studies”, several cases of personal data leakage that had occurred was mentioned. For example, in 2019, there was a case of leakage of personal data from e-commerce company Tokopedia. The personal data, in the form of email addresses, telephone numbers, and residential addresses, were sold at a price of 234 US dollars. Still in the same year, e-commerce Bukalapak also experienced a data leak of approximately 13 million users’ personal data which was stolen by professional hackers known as gnosticplayers. The stolen data consisted of emails, usernames, shopping details, IP addresses, and account passwords. In response to this, Bukalapak has confirmed that there was indeed a hacking attempt, but that no important data such as usernames, passwords, financial or other personal information were obtained by the hackers.
The case of the leak of personal data from this e-commerce company will continue until 2020. Reporting from Kompas.com, in 2020, to be precise, in May, the e-commerce Tokopedia again experienced a leak of personal data. Personal data sold includes e-mail address, username, gender, location, user’s full name, mobile number, and password. However, Tokopedia claims that the user’s information is still protected. In addition, Bhinneka.com, an e-commerce for electronic goods, also experienced the same thing as Tokopedia. Bhinneka.com user data has sold to 1.2 million users in the same month and year. These kind of cases are still happening. As proven in September 2020, the curator of e-commerce, ShopBack, admitted to finding illegal access to the user data system. Although important information is still safe, ShopBack still recommends users change their passwords for account security.
The phenomenon and cases of data leakage from e-commerce were caused due to the changes in people’s behavior through online shopping, which experienced a significant increase. The variety of phenomena and cases impacts e-commerce users, especially the impact on personal data. The personal data of e-commerce users are often threatened and misused by irresponsible parties—it is a particular concern for users in using e-commerce. Thus, the security aspect of data processing needs to be focused by e-commerce companies. Governments and e-commerce users also need to work together to address these issues.
Utilization and Challenges of Big Data for E-Commerce in Indonesia
Some benefits from data in e-commerce business include knowing consumer responses and behavior to the products. It helps to validate and make accurate decisions from many structured data. Information obtained helps improve the company’s image because it knows consumer desires and market trends through data. The use of data in e-commerce provides many benefits and advantages for businesses with a large number of consumers. The company can further develop the system and serve consumers better according to the existing data in the company.
Internet presence has revolutionized the system and various aspects of human life work rapidly and significantly. For the business industry, such as e-commerce companies, the availability of abundant data recorded digitally will be needed for a company’s decision-making. This sea of data leads to one terminology, namely Big Data. Big Data opens opportunities as a business strategy and innovation in processing, analyzing, and storing data with high practical volume and speed (Pujianto, et al., 2018).
Big Data is defined by data with various forms, such as text, numbers, and symbols sourced from facts but yet to have a meaning. The data obtained will be processed into information or the result of data processing both linguistically and mathematically. Big Data refers to three characteristics, namely 3V: volume, variety, velocity, and some add other V elements such as veracity and value (Chandarana, Parth & Vijaya, 2014). Volume or data capacity is the media size of data storage that can accommodate up to zettabytes as IP (internet protocol) based storage capacity. Furthermore, data variation refers to the diversity of data types, while velocity is the speed of processing data generated from the source and in real-time. Meanwhile, veracity and value are related to data uncertainty and the value of resulting information.
The opportunity and use of Big Data are very potential in various business and public sectors. Big Data can be designed and implemented more effectively and precisely to achieve the target simply by paying attention to cyber security and network infrastructure. However, every sophisticated technology concept also has some loopholes in security threats. Therefore, extensive data in Big Data systems also require security from cyber-attacks so that irresponsible parties will not misuse the data.
Criminals can find loopholes in the technology implemented by developers. Technology is the result of product development from human logic. Many criminals take advantage of this loophole as a doorway to collecting data from an organization through a different logical approach. Several data leakage phenomenons show that Indonesia’s digital security level is still low. A data from Veritrans and Daily Social published in 2016 showed that Indonesia was ranked the highest in ten countries most at risk for digital security.
CEO and Chief Digital Forensic Indonesia (DFI), Ruby Alamsyah, said the recent data leaks in some e-commerce sites had a similar pattern. According to Ruby, hackers are targeting e-commerce because their data are vulnerable and in large quantities. In addition, the company has secured passwords with unique hashing algorithms, but they do not optimally secure other personal data. SHA or Secure Hashing Algorithm is a function designed for internet security authority providers to maintain data security (Sinaga, 2019). SHA has different variations according to the level of protection used in data.
How companies optimize their data and keep security threats away is a big data challenge for e-commerce companies. It could be a complex process and should have a good data governance from each company. E-commerce companies must improve data security systems and keep the level of security vulnerabilities at a low percentage. The maturity level in security systems using Big Data technology should continue to be developed by companies that use this technology.
Privacy Threats For E-Commerce Users
The security of personal consumer data in e-commerce should be a guarantee given by the company to their consumers. When consumers feel that e-commerce companies securely protect their data, they will feel secure to use the services provided by the company. However, when viewed from the data security threats in e-commerce companies, the leaked personal data caused consumers to feel a loss of comfort, security, and safety. Therefore, personal data leakage directly poses a privacy threat to consumers who have provided their data to e-commerce companies.
Privacy is crucial for human life because it can maintain every individual’s identity within the boundaries of social life. The role of privacy in people’s social lives regulates information entering and leaving the network and data collection in the community (Richards and King, 2016). Therefore, with the guarantee of privacy by e-commerce companies, consumers can feel safe and comfortable when using the services of e-commerce.
The privacy division in Big Data includes identity protection, equality, security, and trust (Richards and King, 2016). The privacy division in Big Data can make it easier for consumers to demand personal data privacy protection from e-commerce companies. First, identity protection in Big Data can prevent the emergence of recommendations based on analyzing individual behavior and preferences that can limit the space for consumers to move. Second, equality includes restrictions on the collection, algorithmic transparency and accountability, and limits on using analytics to sort and treat people differently. Third, security, namely the existence of a guarantee against the transfer and manipulation of personal consumer data by e-commerce companies or irresponsible outside parties. Fourth, trust is the reciprocity that consumers give to e-commerce companies when they feel that there is a guarantee of security for privacy and personal data that has been shown to the company.
E-Commerce Business Regulations in Indonesia and the Personal Data Protection Bill (RUU PDP)
The people in the community as e-commerce consumers deserve to get information confidentiality protection when it comes to personal data that is prone to be misused. The laws that are used as a reference in running e-commerce in Indonesia, namely Law No. 7 of 2014 regarding Trade, Law No. 11 of 2008 regarding Information and Electronic Transactions, and Law No. 19 of 2016 regarding Information and Electronic Transactions. Apart from these three laws that have been mentioned, there is still a need for a law that regulates personal data protection of the customers.
RUU PDP is one of the regulations that still needs to be passed to regulate personal data protection. The RUU PDP has explaned the meaning of personal data more clearly. In Article 1 Paragraph 1 of the RUU PDP, it is explained about the meaning of personal data that “Personal Data is any data about a person either identified and/or identifiable separately or combined with other information either directly or indirectly through electronic system and/or non-electronic”. Article 1 Paragraph 12 also states that “Violation of Personal Data is a violation of the rights of owners of the personal data based on this law” (DPR RI, 2019). Apart from that, the RUU PDP which regulates several matters regarding the guarantee of a person’s personal data can also underline the importance of this bill to be passed immediately.
Data sovereignty, personal data protection, and the responsibilities of personal data users are some of the things regulated in the RUU PDP. Therefore, the RUU PDP is a draft that can guarantee the preservation of a person’s personal data not to be misused. The types of personal data protected by the RUU PDP based on the third article of the RUU PDP include both personal data that is specific and general. Personal data that is specific is health information data, biometric data, genetic data, sexual orientation, political views, crime records, children’s data, and personal financial data. While personal data that is general is full name, gender, nationality, and religion.
However, the draft that has been included in National Legislation Program (Prolegnas) for two years has bot been ratified. The fate of this draft is still facing an uncertainty even though it has been included in the government’s priority bill. The draft faced many obstacles in the ratification process. Those obstacles are the conflicting interests between government and non-government agencies, the high ego of each institution, and the slow process of discussion because the constant change of inter-agency representatives during the deliberation of the bills (Padma, 2020). Thus, efforts from the government are needed to provide legal certainty and it is necessary for e-commerce companies and the public to be given a thorough understanding of ethics in informational technology so that they can fortify themselves against data leaks that concern privacy.
The idea of protecting one’s right to privacy as important is based on personal respect and values such as individual dignity, autonomy, and personal independence (Reynaldi et al., 2021). When accessing an online shopping website to buy goods makes a virtual crime loophole in work, e-commerce companies should take this issue seriously because it is a real threat to the consumers. Companies engaged in electronic commerce need to maintain and improve the security of consumer personal data with a clear governance for the companies. the RUU PDP is an urgency to better protect the personal data of the Indonesian people for their privacy and its protection–especially when shopping online because the data is prone to be misused.
Authors: May Latifah, Rachel Farahdiba R, and Ratu Mutiara Kalbu
Editor: Irma Hidayah
Illustrator: David Regiasmara Putrawan
Translator: Irma Hidayah
References
Ashari, M. (2019). Keamanan Informasi: Sudah Saatnya Kita Peduli. Kemenkeu.go.id. Accessed 15 March 2021. URL: https://www.djkn.kemenkeu.go.id/kpknl-kisaran/baca-artikel/13113/Keamanan-Informasi-Sudah-Saatnya-Kita-Peduli.html
Chandarana, Parth, & Vijayalakshmi, M. (2014). Big Data analytics frameworks: Circuits, Systems, Communication and Information Technology Applications (CSCITA). In International Conference on IEEE 2014. IEEE.Josephine, J., Rosadi, Sinta Dewi., dan Sudaryat. (2020). Perlindungan Konsumen Daring dan Tanggung Jawab Perusahaan Marketplace atas Data Privasi Konsumen. Jurnal Suara Keadilan. 21 (1) : 97-112.
Harahap, Dedy Ansari., & Amanah, D. (2018). Perilaku Belanja Online di Indonesia : Studi Kasus. Jurnal Manajemen Sains Indonesia. 9 (2) : 19-21. Accessed 10 March 2021. URL: http://journal.unj.ac.id/unj/index.php/jrmsi/article/view/6005
Nugroho, Fendy Prasetyo., Abdullah, Robi Wariyanto., Wulandari, S., & Hanafi. (2019). KEAMANAN BIG DATA DI ERA DIGITAL DI INDONESIA. Jurnal Informa : Jurnal Penelitian Dan Pengabdian Masyarakat, 5(1), 28–34. URL: https://doi.org/10.46808/informa.v5i1.65
Laudon, Kenneth C. dan Carol Guercio Traver.( 2014). E-Commerce: Business, Technology & Society 10th edition. New Jersey: Pearson.
Pujianto, A., Mulyati, A., & Novaria, R. (2018). PEMANFAATAN BIG DATA DAN PERLINDUNGAN PRIVASI KONSUMEN DI ERA EKONOMI DIGITAL. Majalah Ilmiah Bijak, 15(2), 127–137. URL: https://doi.org/10.31334/bijak.v15i2.201
Reynaldi, Farah Azzahra., Adika Tifana, N., Muhammad, D., Amelia Hidayat, F., Daffa M. Erlyansyah, R. and Rahma, N. (2021). Urgensi Perlindungan Data Pribadi dalam Menjamin Hak Privasi: Sebuah Telaah RUU Perlindungan Data Pribadi – Fakultas Hukum Universitas Padjadjaran. Fakultas Hukum Universitas Padjadjaran. Accessed 19 March 2021. URL: https://fh.unpad.ac.id/urgensi-perlindungan-data-pribadi-dalam-menjamin-hak-privasi-sebuah-telaah-ruu-perlindungan-data-pribadi/
Rochmawan, Laksono Tri. (2008). Pengantar Ekonomi Mikro. Semarang: Anindya.
Stephanie, C. (2021). 7 Kasus Kebocoran Data yang Terjadi Sepanjang 2020. Accessed 11 Marc 2021, from KOMPAS.com, URL: https://tekno.kompas.com/read/2021/01/01/14260027/7-kasus-kebocoran-data-yang-terjadi-sepanjang-2020?page=all
Sulistiyono Padma, Adi; Widyantari. (2020). “Pelaksanaan Harmonisasi Rancangan Undang-Undang Perlindungan Data Pribadi (Ruu Pdp).” Jurnal Privat Law VIII(Vol 8, No 1 (2020): JANUARI-JUNI): 117–23. Accessed 19 March 2021. URL: https://jurnal.uns.ac.id/privatlaw/article/view/40384.
Eka Syafrina, A. (2018). “Ancaman Privasi Dalam Big Data”. 138–49. Accessed 19 March 2021. URL: https://media.neliti.com/media/publications/272773-none-f83ccc0b.pdf